It-essentials v7.0 Chapter 13 Exam Answers
1. Which two items are used in asymmetric encryption? (Choose two.)
a token
a DES key
a private key *
a public key *
a TPM
2. Which two algorithms are used for hash encoding to guarantee the integrity of data? (Choose two.)
MD5 *
chap checksum
SHA *
VPN
SSL
3. A high technology company has an issue with unauthorized people gaining access into the company by following an authorized employee through the secure entrance. Which two measures could help with this security breach? (Choose two.)
biometrics
employee smart ID
mantrap *
multifactor authentication
security guard that checks IDs *
4. A user receives a phone call from a person who claims to represent IT services and then asks that user for confirmation of username and password for auditing purposes. Which security threat does this phone call represent?
DDoS
spam
social engineering *
anonymous keylogging
5. The IT department is reporting that a company web server is receiving an abnormally high number of web page requests from different locations simultaneously. Which type of security attack is occurring?
adware
DDoS *
phishing
social engineering
spyware
6. After confirming the removal of a virus from a computer, how should the technician ensure and verify the full functionality of the system?
Check for the latest OS patches and updates. *
Document the problem and the procedures performed to solve it.
Talk with the user to determine the cause of the problem.
Gather information from a number of sources to clearly identify the problem.
7. A system administrator has been asked to protect the sensitive data on the Windows 7 computers of all management employees. Which Windows feature can be used to selectively encrypt individual files within the user accounts of each manager?
BitLocker
EFS *
TPM
Windows Update
8. When would a PC repair person want to deploy the idle timeout feature?
when users are inserting media and running applications not sanctioned by the company
when users are leaving their desk but remaining logged on *
when users are playing music CDs and leaving them playing even after the users have left for the day
when users are surfing the Internet and not doing their job
9. Which type of firewall serves as a relay between users and servers on the Internet, inspects all traffic, and allows or denies traffic based on a set of rules?
packet filtering firewall
stateful packet firewall
proxy firewall *
operating system firewall
10. What would cause a Microsoft Windows update to fail?
The wired or wireless NIC was disabled.
The computer has a virus.
The computer has had its security breached.
A required prior update was not installed. *
11. A user calls the help desk reporting that a laptop is not performing as expected. Upon checking the laptop, a technician notices that some system files have been renamed and file permissions have changed. What could cause these problems?
The file system is corrupted.
The laptop is infected by a virus. *
The display driver is corrupted.
The file system has been encrypted.
12. How can users working on a shared computer keep their personal browsing history hidden from other workers that may use this computer?
Reboot the computer after closing the web browser.
Operate the web browser in private browser mode. *
Use only an encrypted connection to access websites.
Move any downloaded files to the recycle bin.
13. A retail store wants to secure laptops that are on display. The store manager also wants a record of which employees enter the backroom where inventory is kept. Which security option would work best for this situation?
guards and log sheets
security cameras and only the manager having access to the backroom
cable locks and a token-based lock on the backroom *
a condition that laptops are viewed one at a time and only the owner has a key to the backroom
14. Refer to the exhibit.
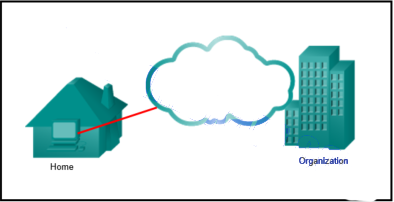
It-essentials v7 Chapter 13 Exam Answers q14
The security policy of an organization allows employees to connect to the office intranet from their homes. Which type of security policy is this?
acceptable use
incident handling
network maintenance
remote access *
15. A user notices that files created and saved locally last week are missing and asks the technician to investigate. The technician suspects there has been a security breach. Which type of malware could be responsible?
adware
phishing
spyware
Trojan *
16. A group of users on the same network are all complaining about their computers running slowly. After investigating, the technician determines that these computers are part of a zombie network. Which type of malware is used to control these computers?
botnet *
rootkit
spyware
virus
17. What are signatures as they relate to security threats?
a unique encryption code used by a known attacker
one or more code patterns within a specific type of malware *
the beginning or end of a malware segment that has a specific cyclic redundancy check number
the checksum associated with each specific type of malware that is stored in a virus table
18. A college student logs onto a college computer for the first time. Which security policy category should be presented to the student?
acceptable use policies *
identification and authentication policies
incident handling policies
network maintenance policies
19. A technician is preparing to encrypt a corporate drive by using Microsoft BitLocker. Which BIOS option will the technician need to enable?
NTFS
SSL
TPM *
EFS
20. Which security technique or device wipes the data from a hard drive by being placed near the drive platter for at least 2 minutes?
degaussing wand *
EFS
low-level format
biometric scanner
erase scope
21. Refer to the exhibit.
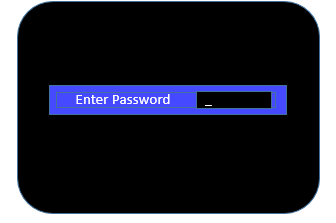
It-essentials v7 Chapter 13 Exam Answers q21
Which type of workstation password is being used?
BIOS *
login
multifactor
network
synchronous
22. A customer uses Internet Explorer and Microsoft Edge as browsers on the computer. The customer asks the technician how to configure the computer to detect and filter phishing websites, to analyze websites for suspicious items, and to check downloads against a list of known malicious files and sites. Which web security feature should the technician demonstrate?
ActiveX Filter
AutoPlay
Firewall
SmartScreen Filter *
23. A SOHO company has hired a technician to come in and configure and secure the computers. The technician has decided to configure a local security policy for the machines. Which setting would the technician use to ensure that the user did not make their password the same as their own user account name?
enforce password history
maximum password age
minimum password length
meet complexity requirements *
24. A technician is configuring rights and permissions in Windows 7. Which tool will the technician use?
Device Manager
Local Security Policy
Local Users and Groups *
Resource Monitor
25. An IT technician wants to create a rule on two Windows 10 computers to prevent an installed application from accessing the public Internet. Which tool would the technician use to accomplish this task?
Computer Management
DMZ
Local Security Policy
Windows Defender Firewall with Advanced Security *
26. A newly created company has fifteen Windows 10 computers that need to be installed before the company can open for business. What is a best practice that the technician should implement when configuring the Windows Firewall?
The technician should remove all default firewall rules and selectively deny traffic from reaching the company network.
The technician should enable the Windows Firewall for inbound traffic and install other firewall software for outbound traffic control.
After implementing third party security software for the company, the technician should verify that the Windows Firewall is disabled. *
The technician should create instructions for corporate users on how to allow an app through the WIndows Firewall using the Administrator account.
27. Which two statements characterize wireless network security? (Choose two.)
Wireless networks offer the same security features as wired networks offer.
Wireless guest mode provides open access to a protected LAN.
With SSID broadcast disabled, an attacker must know the SSID to connect. *
Using the default IP address on an access point makes hacking easier. *
An attacker needs physical access to at least one network device to launch an attack.
28. A manager approaches a PC repair person with the issue that users are coming in to the company in the middle of the night to play games on their computers. What might the PC repair person do to help in this situation?
Limit the login times. *
Use Event View to document the times logged in and out of the computer.
Use Device Manager to limit access to the computer.
Enable power on passwords in the BIOS.
29. A technician has been asked by a manager to recommend a security solution for protecting a computer against worms. Which security technique should the technician recommend?
antimalware *
SSL
ping sweep
IPS
30. A technician has been asked by a manager to recommend a security solution for protecting a computer against ransomware. Which security technique should the technician recommend?
antimalware *
encryption
ping sweep
IPS
31. A technician has been asked by a manager to recommend a security solution for protecting a computer against spyware. Which security technique should the technician recommend?
antimalware *
dual authentication
ping sweep
IPS
32. A technician has been asked by a manager to recommend a security solution for protecting a computer against keyloggers. Which security technique should the technician recommend?
antimalware *
ASA
ping sweep
IPS
33. A technician has been asked by a manager to recommend a security solution for protecting a computer against adware programs. Which security technique should the technician recommend?
antimalware *
IPS
ping sweep
ASA
34. A technician has been asked by a manager to recommend a security solution for protecting a computer against rootkits. Which security technique should the technician recommend?
antimalware *
ping sweep
dual authentication
ASA
35. A technician has been asked by a manager to recommend a security solution for protecting a computer against Trojans. Which security technique should the technician recommend?
antimalware *
port scan
dual authentication
ASA
