CCNA 1 v7.0 Modules 14 – 15: Network Application Communications Exam Answers 2020
1. Which action is performed by a client when establishing communication with a server via the use of UDP at the transport layer?
The client sets the window size for the session.
The client sends an ISN to the server to start the 3-way handshake.
The client randomly selects a source port number.*
The client sends a synchronization segment to begin the session.
2. Which transport layer feature is used to guarantee session establishment?
UDP ACK flag
TCP 3-way handshake*
UDP sequence number
TCP port number
3. What is the complete range of TCP and UDP well-known ports?
0 to 255
0 to 1023*
256 – 1023
1024 – 49151
4. What is a socket?
the combination of the source and destination IP address and source and destination Ethernet address
the combination of a source IP address and port number or a destination IP address and port number*
the combination of the source and destination sequence and acknowledgment numbers
the combination of the source and destination sequence numbers and port numbers
5. A PC is downloading a large file from a server. The TCP window is 1000 bytes. The server is sending the file using 100-byte segments. How many segments will the server send before it requires an acknowledgment from the PC?
1 segment
10 segments*
100 segments
1000 segments
6. Which factor determines TCP window size?
the amount of data to be transmitted
the number of services included in the TCP segment
the amount of data the destination can process at one time*
the amount of data the source is capable of sending at one time
7. What does a client do when it has UDP datagrams to send?
It just sends the datagrams.*
It queries the server to see if it is ready to receive data.
It sends a simplified three-way handshake to the server.
It sends to the server a segment with the SYN flag set to synchronize the conversation.
8. Which three fields are used in a UDP segment header? (Choose three.)
Window Size
Length*
Source Port*
Acknowledgment Number
Checksum*
Sequence Number
9. What are two roles of the transport layer in data communication on a network? (Choose two.)
identifying the proper application for each communication stream
tracking the individual communication between applications on the source and destination hosts*
providing frame delimiting to identify bits making up a frame
performing a cyclic redundancy check on the frame for errors
providing the interface between applications and the underlying network over which messages are transmitted
10. What information is used by TCP to reassemble and reorder received segments?
port numbers
sequence numbers*
acknowledgment numbers
fragment numbers
11. What important information is added to the TCP/IP transport layer header to ensure communication and connectivity with a remote network device?
timing and synchronization
destination and source port numbers*
destination and source physical addresses
destination and source logical network addresses
12. Which two characteristics are associated with UDP sessions? (Choose two.)
Destination devices receive traffic with minimal delay.*
Transmitted data segments are tracked.
Destination devices reassemble messages and pass them to an application.
Received data is unacknowledged.*
Unacknowledged data packets are retransmitted.
13. A client application needs to terminate a TCP communication session with a server. Place the termination process steps in the order that they will occur. (Not all options are used.)
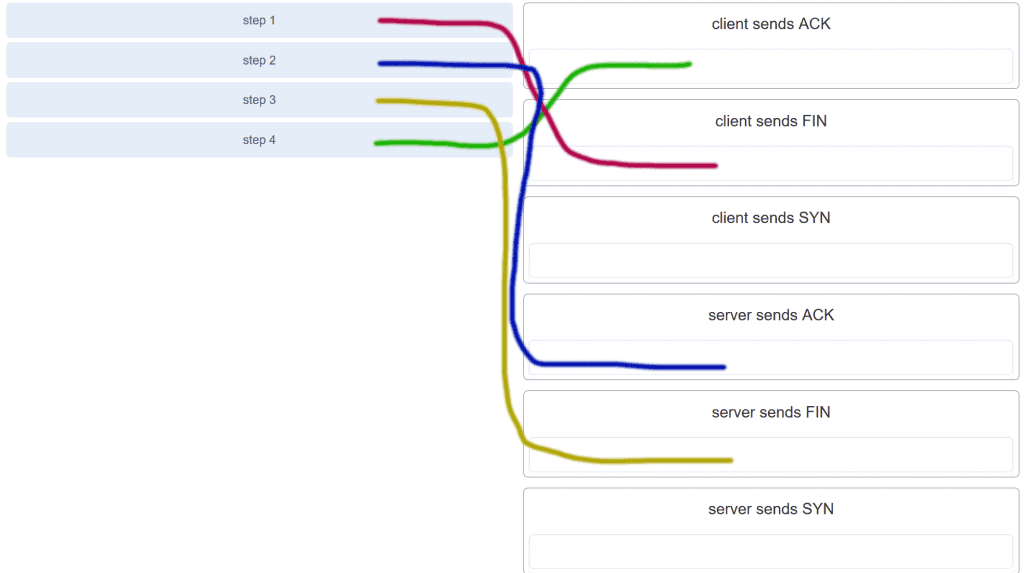
CCNA 1 v7.0 Modules 14 – 15 Exam Answers p13
14. Which flag in the TCP header is used in response to a received FIN in order to terminate connectivity between two network devices?
FIN
ACK*
SYN
RST
15. Which protocol or service uses UDP for a client-to-server communication and TCP for server-to-server communication?
HTTP
FTP
DNS*
SMTP
16. What is a characteristic of UDP?
UDP datagrams take the same path and arrive in the correct order at the destination.
Applications that use UDP are always considered unreliable.
UDP reassembles the received datagrams in the order they were received.*
UDP only passes data to the network when the destination is ready to receive the data.
17. What kind of port must be requested from IANA in order to be used with a specific application?
registered port*
private port
dynamic port
source port
18. Which three application layer protocols use TCP? (Choose three.)
SMTP*
FTP*
SNMP
HTTP*
TFTP
DHCP
19. Which three statements characterize UDP? (Choose three.)
UDP provides basic connectionless transport layer functions.*
UDP provides connection-oriented, fast transport of data at Layer 3.
UDP relies on application layer protocols for error detection.*
UDP is a low overhead protocol that does not provide sequencing or flow control mechanisms.*
UDP relies on IP for error detection and recovery.
UDP provides sophisticated flow control mechanisms.
20. Which two fields are included in the TCP header but not in the UDP header? (Choose two.)
Window*
checksum
source port
destination port
sequence number*
21. Which field in the TCP header indicates the status of the three-way handshake process?
window
reserved
checksum
control bits*
22. Why does HTTP use TCP as the transport layer protocol?
to ensure the fastest possible download speed
because HTTP is a best-effort protocol
because transmission errors can be tolerated easily
because HTTP requires reliable delivery*
23. Which two types of applications are best suited for UDP? (Choose two.)
applications that need data flow control
applications that require reliable delivery
applications that handle reliability themselves*
applications that need the reordering of segments
applications that can tolerate some data loss, but require little or no delay*
24. How are port numbers used in the TCP/IP encapsulation process?
Source port numbers and destination port numbers are not necessary when UDP is the transport layer protocol being used for the communication.
Source port and destination port numbers are randomly generated.
If multiple conversations occur that are using the same service, the source port number is used to track the separate conversations.*
Destination port numbers are assigned automatically and cannot be changed.
25. In what two situations would UDP be better than TCP as the preferred transport protocol? (Choose two.)
when applications need to guarantee that a packet arrives intact, in sequence, and unduplicated
when a faster delivery mechanism is needed*
when delivery overhead is not an issue
when applications do not need to guarantee delivery of the data*
when destination port numbers are dynamic
26. What are three responsibilities of the transport layer? (Choose three.)
meeting the reliability requirements of applications, if any*
multiplexing multiple communication streams from many users or applications on the same network*
identifying the applications and services on the client and server that should handle transmitted data*
directing packets towards the destination network
formatting data into a compatible form for receipt by the destination devices
conducting error detection of the contents in frames
27. Which three statements describe a DHCP Discover message? (Choose three.)
The source MAC address is 48 ones (FF-FF-FF-FF-FF-FF).
The destination IP address is 255.255.255.255.*
The message comes from a server offering an IP address.
The message comes from a client seeking an IP address.*
All hosts receive the message, but only a DHCP server replies.*
Only the DHCP server receives the message.
28. Which two protocols may devices use in the application process that sends email? (Choose two.)
HTTP
SMTP*
POP
IMAP
DNS*
POP3
29. What is true about the Server Message Block protocol?
Different SMB message types have a different format.
Clients establish a long term connection to servers.*
SMB messages cannot authenticate a session.
SMB uses the FTP protocol for communication.
30. What is the function of the HTTP GET message?
to request an HTML page from a web server*
to send error information from a web server to a web client
to upload content to a web server from a web client
to retrieve client email from an email server using TCP port 110
31. Which OSI layer provides the interface between the applications used to communicate and the underlying network over which messages are transmitted?
Application*
presentation
session
transport
32. Which networking model is being used when an author uploads one chapter document to a file server of a book publisher?
peer-to-peer
master-slave
client/server*
point-to-point
33. What do the client/server and peer-to-peer network models have in common?
Both models have dedicated servers.
Both models support devices in server and client roles.*
Both models require the use of TCP/IP-based protocols.
Both models are used only in the wired network environment.
34. In what networking model would eDonkey, eMule, BitTorrent, Bitcoin, and LionShare be used?
peer-to-peer*
client-based
master-slave
point-to-point
35. What is a common protocol that is used with peer-to-peer applications such as WireShare, Bearshare, and Shareaza?
Ethernet
Gnutella*
POP
SMTP
36. What is a key characteristic of the peer-to-peer networking model?
wireless networking
social networking without the Internet
network printing using a print server
resource sharing without a dedicated server*
37. The application layer of the TCP/IP model performs the functions of what three layers of the OSI model? (Choose three.)
physical
sesión*
network
presentation*
data link
transport
application*
38. What is an example of network communication that uses the client-server model?
A user uses eMule to download a file that is shared by a friend after the file location is determined.
A workstation initiates an ARP to find the MAC address of a receiving host.
A user prints a document by using a printer that is attached to a workstation of a coworker.
A workstation initiates a DNS request when the user types www.cisco.com in the address bar of a web browser.*
39. Which layer in the TCP/IP model is used for formatting, compressing, and encrypting data?
internetwork
session
presentation
application*
network access
40. What is an advantage of SMB over FTP?
Only with SMB can data transfers occur in both directions.
Only SMB establishes two simultaneous connections with the client, making the data transfer faster.
SMB is more reliable than FTP because SMB uses TCP and FTP uses UDP.
SMB clients can establish a long-term connection to the server.*
41. A manufacturing company subscribes to certain hosted services from its ISP. The services that are required include hosted world wide web, file transfer, and e-mail. Which protocols represent these three key applications? (Choose three.)
FTP*
HTTP*
DNS
SNMP
DHCP
SMTP*
42. Which application layer protocol uses message types such as GET, PUT, and POST?
DNS
DHCP
SMTP
HTTP*
POP3
43. What type of information is contained in a DNS MX record?
the FQDN of the alias used to identify a service
the IP address for an FQDN entry
the domain name mapped to mail exchange servers*
the IP address of an authoritative name server
44. Which three protocols operate at the application layer of the TCP/IP model? (Choose three.)
ARP
TCP
UDP
FTP*
POP3*
DHCP*
45. Which protocol is used by a client to communicate securely with a web server?
SMTP
SMB
IMAP
HTTPS*
46. Which applications or services allow hosts to act as client and server at the same time?
client/server applications
email applications
P2P applications*
authentication services
47. What are two characteristics of peer-to-peer networks? (Choose two.)
scalability
one way data flow
decentralized resources*
centralized user accounts
resource sharing without a dedicated server*
48. Which scenario describes a function provided by the transport layer?
A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.*
A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
49. Which three layers of the OSI model provide similar network services to those provided by the application layer of the TCP/IP model? (Choose three.)
physical layer
session layer*
transport layer
application layer*
presentation layer*
data link layer
50. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received two packets of data from the PC?
3001*
6001
4500
6000
51. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received three packets of data from the PC?
4501*
6001
6000
4500
52. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received four packets of data from the PC?
6001*
3001
1501
1500
53. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received four packets of data from the PC?
6001*
3001
3000
1500
54. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received two packets of data from the PC?
3001*
4501
3000
1500
55. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received two packets of data from the PC?
3001*
4501
4500
1500
56. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received two packets of data from the PC?
3001*
6001
4500
3000
57. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received two packets of data from the PC?
3001*
6001
6000
3000
58. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received three packets of data from the PC?
4501*
6001
6000
3000
59. A PC that is communicating with a web server has a TCP window size of 6,000 bytes when sending data and a packet size of 1,500 bytes. Which byte of information will the web server acknowledge after it has received three packets of data from the PC?
4501*
6001
1500
4500
60. A client creates a packet to send to a server. The client is requesting TFTP service. What number will be used as the destination port number in the sending packet?
69*
67
53
80
61. A client creates a packet to send to a server. The client is requesting FTP service. What number will be used as the destination port number in the sending packet?
21*
69
67
80
62. A client creates a packet to send to a server. The client is requesting SSH service. What number will be used as the destination port number in the sending packet?
22*
69
67
80
63. A client creates a packet to send to a server. The client is requesting HTTP service. What number will be used as the destination port number in the sending packet?
80*
67
53
69
64. A client creates a packet to send to a server. The client is requesting POP3 service. What number will be used as the destination port number in the sending packet?
110*
67
53
69
65. A client creates a packet to send to a server. The client is requesting telnet service. What number will be used as the destination port number in the sending packet?
23*
443
161
110
66. A client creates a packet to send to a server. The client is requesting POP3 service. What number will be used as the destination port number in the sending packet?
110*
443
161
80
67. A client creates a packet to send to a server. The client is requesting SNMP service. What number will be used as the destination port number in the sending packet?
161*
443
110
80
68. A client creates a packet to send to a server. The client is requesting SMTP service. What number will be used as the destination port number in the sending packet?
25*
443
161
110
69. A client creates a packet to send to a server. The client is requesting HTTPS service. What number will be used as the destination port number in the sending packet?
443*
161
110
80
Modules 14 – 15: Network Application Communications Exam Answers (Additional)
1. Which action is performed by a client when establishing communication with a server via the use of UDP at the transport layer?
The client sets the window size for the session.
The client sends an ISN to the server to start the 3-way handshake.
The client randomly selects a source port number.*
The client sends a synchronization segment to begin the session.
2. Which transport layer feature is used to guarantee session establishment?
UDP ACK flag
TCP 3-way handshake*
UDP sequence number
TCP port number
3. What is the complete range of TCP and UDP well-known ports?
0 to 255
0 to 1023*
256 – 1023
1024 – 49151
4. What is a socket?
the combination of the source and destination IP address and source and destination Ethernet address
the combination of a source IP address and port number or a destination IP address and port number*
the combination of the source and destination sequence and acknowledgment numbers
the combination of the source and destination sequence numbers and port numbers
5. How does a networked server manage requests from multiple clients for different services?
The server sends all requests through a default gateway.
Each request is assigned source and destination port numbers.*
The server uses IP addresses to identify different services.
Each request is tracked through the physical address of the client.
6. Which two services or protocols use the preferred UDP protocol for fast transmission and low overhead? (Choose two)
FTP
DNS*
HTTP
POP3
VoIP*
7. What is the purpose of using a source port number in a TCP communication?
to notify the remote device that the conversation is over
to assemble the segments that arrived out of order
to keep track of multiple conversations between devices*
to inquire for a nonreceived segment
8. Which number or set of numbers represents a socket?
01-23-45-67-89-AB
21
192.168.1.1:80*
10.1.1.15
9. Which two flags in the TCP header are used in a TCP three-way handshake to establish connectivity between two network devices? (Choose two.)
ACK*
FIN
PSH
RST
SYN*
URG
10. What happens if part of an FTP message is not delivered to the destination?
The message is lost because FTP does not use a reliable delivery method.
The FTP source host sends a query to the destination host.
The part of the FTP message that was lost is re-sent.*
The entire FTP message is re-sent.
11. What type of applications are best suited for using UDP?
applications that are sensitive to delay*
applications that need reliable delivery
applications that require retransmission of lost segments
applications that are sensitive to packet loss
12. Network congestion has resulted in the source learning of the loss of TCP segments that were sent to the destination. What is one way that the TCP protocol addresses this?
The source decreases the amount of data that it transmits before it receives an acknowledgement from the destination.*
The source decreases the window size to decrease the rate of transmission from the destination.
The destination decreases the window size.
The destination sends fewer acknowledgement messages in order to conserve bandwidth.
13. Which two operations are provided by TCP but not by UDP? (Choose two.)
identifying the applications
acknowledging received data*
tracking individual conversations
retransmitting any unacknowledged data*
reconstructing data in the order received
14. What is the TCP mechanism used in congestion avoidance ?
three-way handshake
socket pair
two-way handshake
sliding window*
15. What is a responsibility of transport layer protocols?
providing network access
tracking individual conversations*
determining the best path to forward a packet
translating private IP addresses to public IP addresses
16. Which protocol can be used to transfer messages from an email server to an email client?
SMTP
POP3*
SNMP
HTTP
17. When retrieving email messages, which protocol allows for easy, centralized storage and backup of emails that would be desirable for a small- to medium-sized business?
IMAP*
POP
SMTP
HTTPS
18. Which application layer protocol is used to provide file-sharing and print services to Microsoft applications?
HTTP
SMTP
DHCP
SMB*
19. An author is uploading one chapter document from a personal computer to a file server of a book publisher. What role is the personal computer assuming in this network model?
Client*
master
server
slave
transient
20. Which statement is true about FTP?
The client can choose if FTP is going to establish one or two connections with the server.
The client can download data from or upload data to the server.*
FTP is a peer-to-peer application.
FTP does not provide reliability during data transmission.
21. A wireless host needs to request an IP address. What protocol would be used to process the request?
FTP
HTTP
DHCP*
ICMP
SNMP
22. Which TCP/IP model layer is closest to the end user?
Application*
internet
network access
transport
23. Which three protocols or standards are used at the application layer of the TCP/IP model? (Choose three.)
TCP
HTTP*
MPEG*
GIF*
IP
UDP
24. Which protocol uses encryption?
DHCP
DNS
FTP
HTTPS*
25. Why is DHCP preferred for use on large networks?
Large networks send more requests for domain to IP address resolution than do smaller networks.
DHCP uses a reliable transport layer protocol.
It prevents sharing of files that are copyrighted.
It is a more efficient way to manage IP addresses than static address assignment.*
Hosts on large networks require more IP addressing configuration settings than hosts on small networks.
26. Which two tasks can be performed by a local DNS server? (Choose two.)
providing IP addresses to local hosts
allowing data transfer between two network devices
mapping name-to-IP addresses for internal hosts*
forwarding name resolution requests between servers*
retrieving email messages
27. On a home network, which device is most likely to provide dynamic IP addressing to clients on the home network?
a dedicated file server
a home router*
an ISP DHCP server
a DNS server
28. What part of the URL, http://www.cisco.com/index.html, represents the top-level DNS domain?
.com*
www
http
index
29. What are two characteristics of the application layer of the TCP/IP model? (Choose two.)
responsibility for logical addressing
responsibility for physical addressing
the creation and maintenance of dialogue between source and destination applications*
closest to the end user*
the establishing of window size
30. What message type is used by an HTTP client to request data from a web server?
GET*
POST
PUT
ACK



DEvnet Final Exam – Question – Need the answers
2 – how can a webex teams administrator retrives additional details about a user through API call?
a) By using value of the person id key in the API cal
b)By using the value of the organization name in the API cal
c)By using the value of a webex teams registered email address in the API cal
d)By using the value of orgId in the API cal
5 – what is an example of a use supported by Cisco UCS Director and UCS Manager?
a) call center and cal management over IP network
b) underlying central system workflow management and migration
C) bare metal server provisioning and monitoring of virtual enviroments
d) telemetry data colletion and analysis
6 – which programming language is supported by the webex xAPI to develop macros for on-device customization?
a) JavaScript
b)Java
c)Python
d) C++
7 – which library is most commonly used Python Library for connecting NETCONF clients with a NETCONF server?
a)pyclient
b)posix
c)ncclient
d)pypi
8 – which cisco SDK works with ACI?
a)UCS
b)IMC
c)Instant connect
d)Cobra
10 – wich Devnet resource would a developer use in order to test custom code in a production-like enviroment?
a)Devnet support
b)Devnet learning labs
c)Devnet Sandbox
d)code Exchange
11 – which devnet resource would a developer use to look for a python library that supports for a specific Cisco product?
a)Code Exchange
b)Devnet sandbox
c)Devnet learning labs
d)Devnet support
13 – which three avenues are available within devnet for developers who need help with specfic developer sceneario question concerning Cisco products?(choose three)
a)Posting to a webex teams space
b)Posting on the cisco learning network
c)Posting to the devnet zone
d)Posting to a community fórum
e)Posting to a news group
f)Logging a ticket
14 – what platforms are provided by devnet for community members to share solutions,tools kits, and other reources with each other?
a)Sandboxes
b)Communities
c)Exchanges
d)Forums
15 – How do API affect traditional IT tasks?
a)They are used to increase computer processing speed and lower power consuption
b)They are used to eliminate repetitive manual tasks and replace them with automation
c)They are used to increase hardware speed and lower power consuption
d)They are used to replace network infrastructure and implementing network virtualization
16 – A student who is interested in networking programmability approaches an instructor for a advice on learning more about the subject. The student is a kinesthetic learner who learns by doing. Which devnet resource should the instructor consider telling the student about?
Devnet zone
Devnet create
Devnet express
Devnet learning labs
18 – How is an ethernet MAC address constructed?
– The first 3 bytes represent the vendor OUI, and the last 3 bytes are assigned randomly by the operating system
– The first 3 bytes represente the network upon which the host resides, and the last 3 bytes uniquely indentify the host
– The first 3 bytes represent the vendor OUI, and last 3 bytes are assigned uniquely by the vendor
– The first 3 bytes are uniquely assigned by IANA, and the last 3 bytes represente the serial number of the host
23 Which command is used to create a new Git repositor?
a)git commit
b)git clone
c)git init
d)git add
24 – which stakeholder determines the useful value of software product features in the Lean process?
a) the programmer
b)the reviewer
c)the customer
d)the scrum master
25 – what is a principle of the Lean software development model?
a) adding additional product features that the costumer did not ask for so that the customer is getting more than expected
b) ordering workers to do tasks they may not want to ensure they get done
c) assigning resources to multiple projects so that effort can be divided on more than one task at time
d) making decisions as late as possible in the proccess so that more facts and details are available
26 – which string of characters is used to identify the begining of a new separate document when multiple documents are in a single YAML file?
a)three dashes “—“
b) three dots “…”
c) three slashes “///”
d) tree pound signs “###”
27 – which convention is used in python to indicate that methods and variables in a class are private and not to be used outsider of the class?
a) by using the command class private classname(): to start the class definition
b) by using a single preceding underscore (_) for a method or variable
c) by declaring a private method or variable in the begining of the class definition
d) by using two preceding hyphens(–) for a method or variable
28 – which convention is used in python to indicate that methods and variables in a class are private and not to be used outsider of the class?
a) by using the command class private classname(): to start the class definition
b) by using a single preceding underscore (_) for a method or variable
c) by declaring a private method or variable in the begining of the class definition
d) by using two preceding hyphens(–) for a method or variable
29 – which git command is used to compare changes between files?
a)git checkout
b)git merge
c)git status
d)git diff
30 – in wich SDLC phase is the software product installed into the production enviroment to decide if i tis ready for release?
a) testing
b) (deployment)
c) design
d) implementation
31 – A packet is received by a server . The packet has a destination port number 443. What protocolo r service is required?
a)HTTPS
b)DHCP
c)HTP
d)NTP
32 – a network engineer is creating a Docker container using the docker build command. If the engineer does not specify a tag, wich tag will be used by default?
a) default
b) latest
c)tag
d)(a blank space)
33 – which scenario exbits the social proof principle of human influence?
a)A user opens an email advertising a free trial on a website that is only available for a few hours
b)A user receive a phone cal from someone claiming to be from IT department who needs to verify credentials
c)A user completes a survey requesting personal information after seeing co-workers completing the survey
d)A user visits a web site ofering free gift if the user provides contact information
36 – what are two characteristis os staging enviroment of the four-tier deployment enviroment structure?(choose two)
a) i tis where end users will interact with the code
b) it is the point where code has been tested multiple times and is error free
c) it is strutured as close as possible to the actual production enviroment
d) it is where the code undergoes final acceptance testing in a realistic enviroment
e) it oftem includes automated testing tools such as jenkins,CircleCI, or Travis CI
37 – Which SQL injection defense method should be used only as a last resort?
a)Using parameterized queries
b)Implementing whitelisted input validation
c)Escaping all user-supplied input **
d)Using database firewall
38 – which technique is used to make the output of password hashing nondeterministic?
a)Password strength validation tools
b)Password salting **
c)Multifactor authentication
d)Password length and complexity
41 – a componente was created with the intente of combining the disciplines and skills of Dev and Ops. This componente created a new job role and implemented a best pratices playbook for doing Ops with software methods. Which componente matches this description?
a)The SRE approach
b)Automated infrastructure
c)Agile infrastructure and operations
d)Shared version control
42 – What is immutable infrastructure in Devops?
a) Insfrastructure that is only deployed and maintained in containers
b) Infrastructure that is deployed with all componente versions locked except for the ability to perform manual configuration changes
c) virtualized insfrastruture that is deployed as golden images
d) insfrastructure that is entirely maintained and deployed in code and never subjected to manual changes
43 – what does self-service refer to in the context of enterprise IT?
a)Imaging frequently used server configuration for rapid deployment
b)Mainstreamed process that promote a lower IT headcount by implemting automation
c)Distribuiting and implementing broad access to a public cloud infrastruture-as-a-service services
d)Automated tools and methods that deliver preconfigured developer platforms on demand
44 – what are two characteristic os stateless applications? (choose two)
a)They can be freely scaled accross capacity without disrupting ongoing customer connections
b)They can store a user state in an acessible database separate from application servers and componentes
c)They can be scaled only by deploying them and destroying the data that users or operators previously needed
d)They must run on container orchestrators like kubernetes
e)They maintain the user state within the local user machine so that automation can work non-destructively
45 – what is a function provided by an implementation of read-only automation solution?
a) the ability to use GET and SET requests to retrieve and send data accross the network insfrastruture
b) the ability to use an automated request to audit configurations and manualy changes in order to implemente compliance
c) the ability to reduce risk by implementing security policies accross the network infrastructure via automated changes
d)the ability to implement network insfrastucture that receives a configuration from specific centralized server
46 – which communicatio protocol does Ansible uses to connect to remote devices?
a)HTTPS
b)Telnet over VPN
c)SSH
d)Secure FTP
47 – which statement describes the term orchestration in IT automation?
a)Orchestration is the building, arranging, integration, and preparation of multi-component aplication accross multiple nodes
b)Orchestration is the process of preparing a server through the instalation of libraries or daemons
c)Orchestration is aimed at managing workload lifecycles and reacting dynamically to changing conditions in order to optime process
d)Orchestration is the obtaining and provisioning of compute, storage, and netword insfrastructure
48 – what is default Shell commonly used on macOS and Linux?
a)Bourne
b)Csh
c)Bash
d)Tcsh
49 – what is the most common cause of IT outages?
a)an engineer misconfiguring a device or network with manual changes
b)an experienced engineer implenting a configuration using automation
c)an experienced engineer using an open Source product
d)a treat actor targeting the enterprise equipment
50 – a software development company specializes in being able to use whatever software development method their costumer wants to use.one costumer company wants to use Lean method. What is a characteristic of this method?
a)A process that amplifies learning as well as quickly as possible
b)A more traditional software development process as they have used this process in past projects
c)A software development process that has the results of one phase feed into the next phase
d)A software development method that tracks closely with software development life cicle
51 – what is an architectural constraint to wich a true RESTfull API web service must adhere?
a)It operates in stateless way
b)It must operate along with a DNS server
c)It uses HTTPS to transport data
d)It operates as a cloud service
52 – what is an architectural constraint to wich a true RESTfull API web service must adhere?
It allow resource caching
It should be behind a firewall
It must support XML-RPC and JSON-RPC
It operates as a cloud service
56 – – a student is learning network automation by using a REST API. The student sends a request to a network device and receives a response with the status code of 202. What does this status code mean?
a)The request was undestood but has been rejected by this server
b)Because of a server error, the request cannot be fulfilled
c)The request was sucessfully and typically includes a payload
d)The requested has been accepted for processing, but the process has not been completed.
57 – what are two requirements for an aplication to communicate with a webhook provider? (choose two)
a)The host where aplication is running must have na SSH cliente installed
b)The host where aplication is running must have an SSH server running
c)The application must support JSON
d)The application must register URL with the webhook provider
e)The application must always be running
60 – when thinking about the functional places of a network, what is unique about the data plane?
a)It includes applications and protocols used between network devices such as routers
b)If forwards data through a network device such as a router or a switch
c)It includes the SNMP protocol
d)It manupulates traffic using python
i would like to thanks too much bro