CCNA 1 v7.0 Modules 11 – 13: IP Addressing Exam Answers 2020
1. What is the prefix length notation for the subnet mask 255.255.255.224?
/25
/26
/27*
/28
2. How many valid host addresses are available on an IPv4 subnet that is configured with a /26 mask?
254
190
192
62*
64
3. Which subnet mask would be used if 5 host bits are available?
255.255.255.0
255.255.255.128
255.255.255.224*
255.255.255.240
4. A network administrator subnets the 192.168.10.0/24 network into subnets with /26 masks. How many equal-sized subnets are created?
1
2
4*
8
16
64
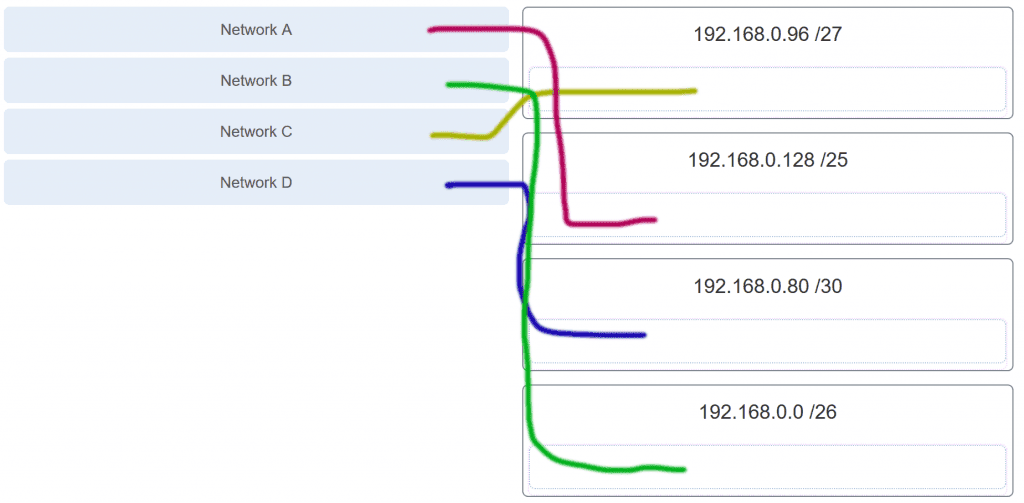
5. Match the subnetwork to a host address that would be included within the subnetwork. (Not all options are used.)

6. An administrator wants to create four subnetworks from the network address 192.168.1.0/24. What is the network address and subnet mask of the second useable subnet?
subnetwork 192.168.1.64
subnet mask 255.255.255.192**
subnetwork 192.168.1.32
subnet mask 255.255.255.240
subnetwork 192.168.1.64
subnet mask 255.255.255.240
subnetwork 192.168.1.128
subnet mask 255.255.255.192
subnetwork 192.168.1.8
subnet mask 255.255.255.224
7. How many bits must be borrowed from the host portion of an address to accommodate a router with five connected networks?
two
three*
four
five
8. How many host addresses are available on the 192.168.10.128/26 network?
30
32
60
62*
64
9. How many host addresses are available on the network 172.16.128.0 with a subnet mask of 255.255.252.0?
510
512
1022*
1024
2046
2048
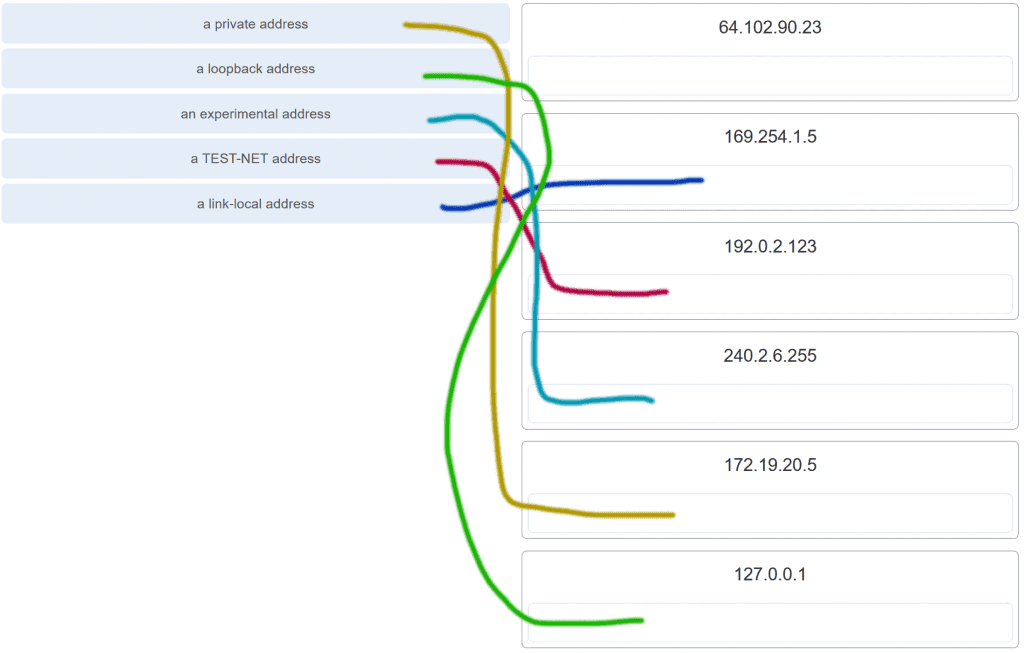
10. Match each IPv4 address to the appropriate address category. (Not all options are used.)

11. What three blocks of addresses are defined by RFC 1918 for private network use? (Choose three.)
10.0.0.0/8*
172.16.0.0/12*
192.168.0.0/16*
100.64.0.0/14
169.254.0.0/16
239.0.0.0/8
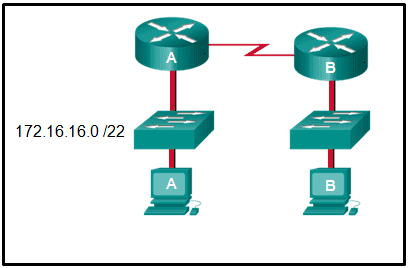
12. Refer to the exhibit.
An administrator must send a message to everyone on the router A network. What is the broadcast address for network 172.16.16.0/22?
172.16.16.255
172.16.20.255
172.16.19.255*
172.16.23.255
172.16.255.255
13. A site administrator has been told that a particular network at the site must accommodate 126 hosts. Which subnet mask would be used that contains the required number of host bits?
255.255.255.0
255.255.255.128*
255.255.255.224
255.255.255.240
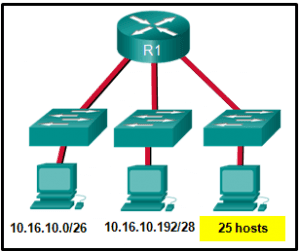
14. Refer to the exhibit.
Considering the addresses already used and having to remain within the 10.16.10.0/24 network range, which subnet address could be assigned to the network containing 25 hosts?
10.16.10.160/26
10.16.10.128/28
10.16.10.64/27*
10.16.10.224/26
10.16.10.240/27
10.16.10.240/28
15. What is the usable number of host IP addresses on a network that has a /26 mask?
256
254
64
62*
32
16
16. Which address prefix range is reserved for IPv4 multicast?
240.0.0.0 – 254.255.255.255
224.0.0.0 – 239.255.255.255*
169.254.0.0 – 169.254.255.255
127.0.0.0 – 127.255.255.255
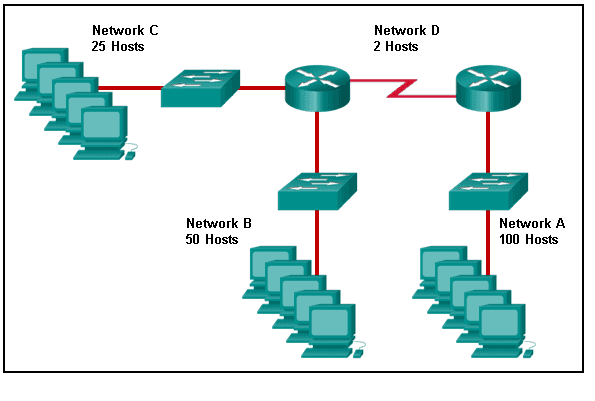
17. Refer to the exhibit.
Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network.
18. A high school in New York (school A) is using videoconferencing technology to establish student interactions with another high school (school B) in Russia. The videoconferencing is conducted between two end devices through the Internet. The network administrator of school A configures the end device with the IP address 209.165.201.10. The administrator sends a request for the IP address for the end device in school B and the response is 192.168.25.10. Neither school is using a VPN. The administrator knows immediately that this IP will not work. Why?
This is a loopback address.
This is a link-local address.
This is a private IP address.*
There is an IP address conflict.
19. Which three addresses are valid public addresses? (Choose three.)
198.133.219.17*
192.168.1.245
10.15.250.5
128.107.12.117*
172.31.1.25
64.104.78.227*
20. A message is sent to all hosts on a remote network. Which type of message is it?
limited broadcast
multicast
directed broadcast*
unicast
21. A company has a network address of 192.168.1.64 with a subnet mask of 255.255.255.192. The company wants to create two subnetworks that would contain 10 hosts and 18 hosts respectively. Which two networks would achieve that? (Choose two.)
192.168.1.16/28
192.168.1.64/27*
192.168.1.128/27
192.168.1.96/28*
192.168.1.192/28
22. Which address is a valid IPv6 link-local unicast address?
FEC8:1::FFFF
FD80::1:1234
FE80::1:4545:6578:ABC1*
FE0A::100:7788:998F
FC90:5678:4251:FFFF
23. Which of these addresses is the shortest abbreviation for the IP address:
3FFE:1044:0000:0000:00AB:0000:0000:0057?
3FFE:1044::AB::57
3FFE:1044::00AB::0057
3FFE:1044:0:0:AB::57*
3FFE:1044:0:0:00AB::0057
3FFE:1044:0000:0000:00AB::57
3FFE:1044:0000:0000:00AB::0057
24. A network administrator has received the IPv6 prefix 2001:DB8::/48 for subnetting. Assuming the administrator does not subnet into the interface ID portion of the address space, how many subnets can the administrator create from the /48 prefix?
16
256
4096
65536*
25. Given IPv6 address prefix 2001:db8::/48, what will be the last subnet that is created if the subnet prefix is changed to /52?
2001:db8:0:f00::/52
2001:db8:0:8000::/52
2001:db8:0:f::/52
2001:db8:0:f000::/52*
26. Consider the following range of addresses:
2001:0DB8:BC15:00A0:0000::
2001:0DB8:BC15:00A1:0000::
2001:0DB8:BC15:00A2:0000::
…
2001:0DB8:BC15:00AF:0000::
The prefix-length for the range of addresses is /60 .
27. What type of IPv6 address is FE80::1?
loopback
link-local*
multicast
global unicast
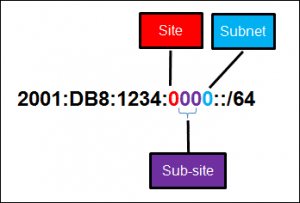
28. Refer to the exhibit.
A company is deploying an IPv6 addressing scheme for its network. The company design document indicates that the subnet portion of the IPv6 addresses is used for the new hierarchical network design, with the site subsection to represent multiple geographical sites of the company, the sub-site section to represent multiple campuses at each site, and the subnet section to indicate each network segment separated by routers. With such a scheme, what is the maximum number of subnets achieved per sub-site?
0
4
16*
256
29. What is used in the EUI-64 process to create an IPv6 interface ID on an IPv6 enabled interface?
the MAC address of the IPv6 enabled interface*
a randomly generated 64-bit hexadecimal address
an IPv6 address that is provided by a DHCPv6 server
an IPv4 address that is configured on the interface
30. What is the prefix for the host address 2001:DB8:BC15:A:12AB::1/64?
2001:DB8:BC15
2001:DB8:BC15:A*
2001:DB8:BC15:A:1
2001:DB8:BC15:A:12
31. An IPv6 enabled device sends a data packet with the destination address of FF02::1. What is the target of this packet?
the one IPv6 device on the link that has been uniquely configured with this address
all IPv6 enabled devices on the local link or network*
only IPv6 DHCP servers
only IPv6 configured routers
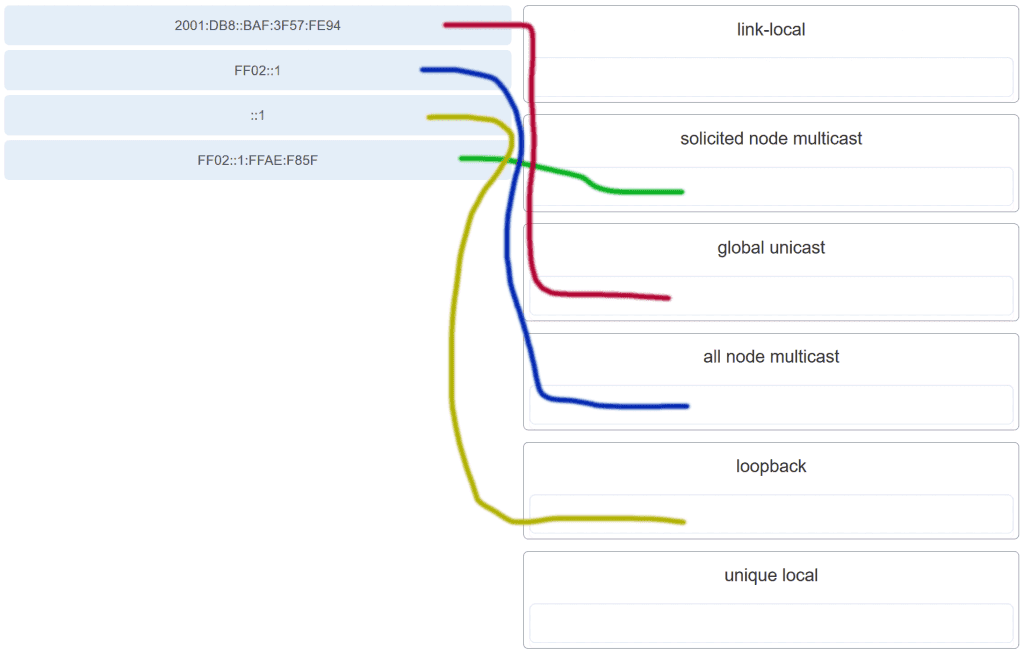
32. Match the IPv6 address with the IPv6 address type. (Not all options are used.)
33. Which IPv6 prefix is reserved for communication between devices on the same link?
FC00::/7
2001::/32
FE80::/10*
FDFF::/7
34. Which type of IPv6 address refers to any unicast address that is assigned to multiple hosts?
unique local
global unicast
link-local
anycast*
35. What are two types of IPv6 unicast addresses? (Choose two.)
multicast
loopback*
link-local*
anycast
broadcast
36. Which service provides dynamic global IPv6 addressing to end devices without using a server that keeps a record of available IPv6 addresses?
stateful DHCPv6
SLAAC*
static IPv6 addressing
stateless DHCPv6
37. Which protocol supports Stateless Address Autoconfiguration (SLAAC) for dynamic assignment of IPv6 addresses to a host?
ARPv6
DHCPv6
ICMPv6*
UDP
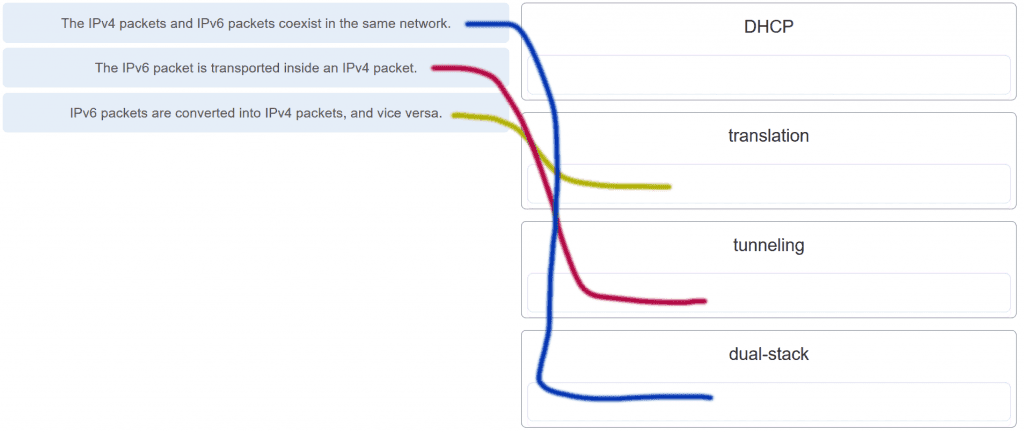
38. Three methods allow IPv6 and IPv4 to co-exist. Match each method with its description. (Not all options are used.)
39. A technician uses the ping 127.0.0.1 command. What is the technician testing?
the TCP/IP stack on a network host*
connectivity between two adjacent Cisco devices
connectivity between a PC and the default gateway
connectivity between two PCs on the same network
physical connectivity of a particular PC and the network
40. Refer to the exhibit.
An administrator is trying to troubleshoot connectivity between PC1 and PC2 and uses the tracert command from PC1 to do it. Based on the displayed output, where should the administrator begin troubleshooting?
PC2
R1*
SW2
R2
SW1
41. Which protocol is used by the traceroute command to send and receive echo-requests and echo-replies?
SNMP
ICMP*
Telnet
TCP
42. Which ICMPv6 message is sent when the IPv6 hop limit field of a packet is decremented to zero and the packet cannot be forwarded?
network unreachable
time exceded*
protocol unreachable
port unreachable
43. A user executes a traceroute over IPv6. At what point would a router in the path to the destination device drop the packet?
when the value of the Hop Limit field reaches 255
when the value of the Hop Limit field reaches zero*
when the router receives an ICMP time exceeded message
when the target host responds with an ICMP echo reply message
44. What is the purpose of ICMP messages?
to inform routers about network topology changes
to ensure the delivery of an IP packet
to provide feedback of IP packet transmissions*
to monitor the process of a domain name to IP address resolution
45. What source IP address does a router use by default when the traceroute command is issued?
the highest configured IP address on the router
a loopback IP address
the IP address of the outbound interface*
the lowest configured IP address on the router
46. Match each description with an appropriate IP address. (Not all options are used.)
47. A user issues a ping 192.135.250.103 command and receives a response that includes a code of 1. What does this code represent?
host unreachable*
protocol unreachable
port unreachable
network unreachable
48. Which subnet would include the address 192.168.1.96 as a usable host address?
192.168.1.64/26*
192.168.1.32/27
192.168.1.32/28
192.168.1.64/29
49. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
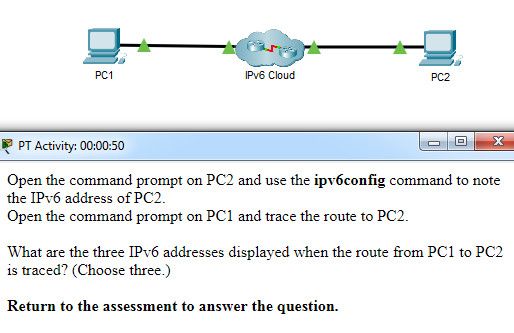
What are the three IPv6 addresses displayed when the route from PC1 to PC2 is traced? (Choose three.)
2001:DB8:1:1::1*
2001:DB8:1:1::A
2001:DB8:1:2::2
2001:DB8:1:2::1*
2001:DB8:1:3::1
2001:DB8:1:3::2*
2001:DB8:1:4::1
50. A host is transmitting a broadcast. Which host or hosts will receive it?
all hosts in the same subnet*
a specially defined group of hosts
the closest neighbor on the same network
all hosts on the Internet
51. A host is transmitting a unicast. Which host or hosts will receive it?
one specific host*
a specially defined group of hosts
all hosts on the Internet
the closest neighbor on the same network
52. A user issues a ping 2001:db8:FACE:39::10 command and receives a response that includes a code of 3. What does this code represent?
address unreachable*
network unreachable
host unreachable
protocol unreachable
53. A host is transmitting a multicast. Which host or hosts will receive it?
a specially defined group of hosts*
one specific host
all hosts with the same IP address
the closest neighbor on the same network
54. A host is transmitting a multicast. Which host or hosts will receive it?
a specially defined group of hosts*
one specific host
directly connected network devices
the closest neighbor on the same network
55. A host is transmitting a multicast. Which host or hosts will receive it?
a specially defined group of hosts*
one specific host
all hosts with the same IP address
all hosts on the Internet
56. A host is transmitting a multicast. Which host or hosts will receive it?
a specially defined group of hosts*
one specific host
directly connected network devices
all hosts on the Internet
57. A host is transmitting a multicast. Which host or hosts will receive it?
a specially defined group of hosts*
all hosts in the same subnet
directly connected network devices
the closest neighbor on the same network
58. A host is transmitting a broadcast. Which host or hosts will receive it?
all hosts in the same subnet*
one specific host
the closest neighbor on the same network
directly connected network devices
59. A host is transmitting a broadcast. Which host or hosts will receive it?
all hosts in the same subnet*
one specific host
all hosts on the Internet
directly connected network devices
60. Which is the compressed format of the IPv6 address 2001:0db8:0000:0000:0000:a0b0:0008:0001?
2001:db8::a0b0:8:1*
2001:db8::ab8:1:0:1000
2001:db80:0:1::80:1
2001:db80:::1::80:1
61. Which is the compressed format of the IPv6 address fe80:09ea:0000:2200:0000:0000:0fe0:0290?
fe80:9ea:0:2200::fe0:290*
fe80:9:20::b000:290
fe80:9ea0::2020:0:bf:e0:9290
fe80:9ea0::2020::bf:e0:9290
62. Which is the compressed format of the IPv6 address 2002:0042:0010:c400:0000:0000:0000:0909?
2002:42:10:c400::909*
200:420:110:c4b::910:0:90
2002:4200::25:1090:0:99
2002:42::25:1090:0:99
63. Which is the compressed format of the IPv6 address 2001:0db8:0000:0000:0ab8:0001:0000:1000?
2001:db8::ab8:1:0:1000*
2001:db8::a0b0:8:1
2001:db8:1::ab8:0:1
2001:db8:0:1::8:1
64. Which is the compressed format of the IPv6 address 2002:0420:00c4:1008:0025:0190:0000:0990?
2002:420:c4:1008:25:190::990*
2002:42:10:c400::909
2002:4200::25:1090:0:99
2002:42::25:1090:0:99
65. Which is the compressed format of the IPv6 address 2001:0db8:0000:0000:0000:a0b0:0008:0001?
2001:db8::a0b0:8:1*
2001:db8:1::ab8:0:1
2001:db8::ab8:1:0:1000
2001:db8:0:1::8:1
66. Which is the compressed format of the IPv6 address fe80:0000:0000:0000:0220:0b3f:f0e0:0029?
fe80::220:b3f:f0e0:29*
fe80:9ea:0:2200::fe0:290
fe80:9ea0::2020:0:bf:e0:9290
fe80:9ea0::2020::bf:e0:9290
67. Which is the compressed format of the IPv6 address 2001:0db8:0000:0000:0000:a0b0:0008:0001?
2001:db8::a0b0:8:1*
2001:db8::ab8:1:0:1000
2001:db80:0:1::80:1
2001:db8:0:1::8:1
68. Which is the compressed format of the IPv6 address 2002:0042:0010:c400:0000:0000:0000:0909?
2002:42:10:c400::909*
2002:4200::25:1090:0:99
2002:420:c4:1008:25:190::990
2002:42::25:1090:0:99
69. Which is the compressed format of the IPv6 address fe80:09ea:0000:2200:0000:0000:0fe0:0290?
fe80:9ea:0:2200::fe0:290*
fe80:9ea0::2020:0:bf:e0:9290
fe80::220:b3f:f0e0:29
fe80::0220:0b3f:f0e0:0029
70. A user issues a ping 2001:db8:FACE:39::10 command and receives a response that includes a code of 2 . What does this code represent?
beyond scope of the source address*
communication with the destination administratively prohibited
address unreachable
no route to destination
71. A user issues a ping 192.135.250.103 command and receives a response that includes a code of 1. What does this code represent?
host unreachable*
beyond scope of the source address
address unreachable
communication with the destination administratively prohibited
72. A user issues a ping fe80:65ab:dcc1::100 command and receives a response that includes a code of 3. What does this code represent?
address unreachable*
communication with the destination administratively prohibited
beyond scope of the source address
no route to destination
73. A user issues a ping 10.10.14.67 command and receives a response that includes a code of 0. What does this code represent?
network unreachable*
protocol unreachable
port unreachable
host unreachable
74. A user issues a ping fe80:65ab:dcc1::100 command and receives a response that includes a code of 4. What does this code represent?
port unreachable*
host unreachable
protocol unreachable
network unreachable
75. A user issues a ping 198.133.219.8 command and receives a response that includes a code of 0. What does this code represent?
network unreachable*
protocol unreachable
port unreachable
host unreachable
76. A user issues a ping 2001:db8:3040:114::88 command and receives a response that includes a code of 4. What does this code represent?
port unreachable*
host unreachable
protocol unreachable
network unreachable
77. A user issues a ping 2001:db8:FACE:39::10 command and receives a response that includes a code of 2. What does this code represent?
beyond scope of the source address*
host unreachable
protocol unreachable
network unreachable
Modules 11 – 13: IP Addressing Exam Answers (Additional)
1. What is the prefix length notation for the subnet mask 255.255.255.224?
/25
/26
/27*
/28
2. How many valid host addresses are available on an IPv4 subnet that is configured with a /26 mask?
254
190
192
62*
64
3. Which subnet mask would be used if 5 host bits are available?
255.255.255.0
255.255.255.128
255.255.255.224*
255.255.255.240
4. A network administrator subnets the 192.168.10.0/24 network into subnets with /26 masks. How many equal-sized subnets are created?
1
2
4*
8
16
64
5. What subnet mask is represented by the slash notation /20?
255.255.255.248
255.255.224.0
255.255.240.0*
255.255.255.0
255.255.255.192
6. Which statement is true about variable-length subnet masking?
Each subnet is the same size.
The size of each subnet may be different, depending on requirements.*
Subnets may only be subnetted one additional time.
Bits are returned, rather than borrowed, to create additional subnets.
7. Why does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
to identify the broadcast address of the destination network
to identify the host address of the destination host
to identify faulty frames
to identify the network address of the destination network*
8. How many usable IP addresses are available on the 192.168.1.0/27 network?
256
254
62
30*
16
32
9. Which subnet mask would be used if exactly 4 host bits are available?
255.255.255.224
255.255.255.128
255.255.255.240*
255.255.255.248
10. Which two parts are components of an IPv4 address? (Choose two.)
subnet portion
network portion*
logical portion
host portion*
physical portion
broadcast portion
11. If a network device has a mask of /26, how many IP addresses are available for hosts on this network?
64
30
62*
32
16
14
12. What does the IP address 172.17.4.250/24 represent?
network address
multicast address
host address*
broadcast address
13. If a network device has a mask of /28, how many IP addresses are available for hosts on this network?
256
254
62
32
16
14*
14. What is the purpose of the subnet mask in conjunction with an IP address?
to uniquely identify a host on a network
to identify whether the address is public or private
to determine the subnet to which the host belongs*
to mask the IP address to outsiders
15. A network administrator is variably subnetting a network. The smallest subnet has a mask of 255.255.255.224. How many usable host addresses will this subnet provide?
2
6
14
30*
62
16. What is indicated by a successful ping to the ::1 IPv6 address?
The host is cabled properly.
The default gateway address is correctly configured.
All hosts on the local link are available.
The link-local address is correctly configured.
IP is properly installed on the host.*
17. What is the most compressed representation of the IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001?
2001:0:abcd::1
2001:0:0:abcd::1*
2001::abcd::1
2001:0000:abcd::1
2001::abcd:0:1
18. What is the purpose of the command ping ::1?
It tests the internal configuration of an IPv6 host.*
It tests the broadcast capability of all hosts on the subnet.
It tests the multicast connectivity to all hosts on the subnet.
It tests the reachability of the default gateway for the network.
19. At a minimum, which address is required on IPv6-enabled interfaces?
link-local*
unique local
site local
global unicast
20. What is the interface ID of the IPv6 address 2001:DB8::1000:A9CD:47FF:FE57:FE94/64?
FE94
FE57:FE94
47FF:FE57:FE94
A9CD:47FF:FE57:FE94*
1000:A9CD:47FF:FE57:FE94
21. What are three parts of an IPv6 global unicast address? (Choose three.)
an interface ID that is used to identify the local network for a particular host
a global routing prefix that is used to identify the network portion of the address that has been provided by an ISP*
a subnet ID that is used to identify networks inside of the local enterprise site*
a global routing prefix that is used to identify the portion of the network address provided by a local administrator
an interface ID that is used to identify the local host on the network*
22. What is the valid most compressed format possible of the IPv6 address 2001:0DB8:0000:AB00:0000:0000:0000:1234?
2001:DB8:0:AB00::1234*
2001:DB8:0:AB::1234
2001:DB8::AB00::1234
2001:DB8:0:AB:0:1234
23. What is the prefix associated with the IPv6 address 2001:CA48:D15:EA:CC44::1/64?
2001::/64
2001:CA48::/64
2001:CA48:D15:EA::/64*
2001:CA48:D15:EA:CC44::/64
24. What type of address is automatically assigned to an interface when IPv6 is enabled on that interface?
global unicast
link-local*
loopback
unique local
25. Which IPv6 network prefix is only intended for local links and can not be routed?
2001::/3
FC00::/7
FE80::/10*
FEC0::/10
26. Your organization is issued the IPv6 prefix of 2001:0000:130F::/48 by your service provider. With this prefix, how many bits are available for your organization to create subnetworks if interface ID bits are not borrowed?
8
16*
80
128
27. What is the subnet address for the IPv6 address 2001:D12:AA04:B5::1/64?
2001::/64
2001:D12::/64
2001:D12:AA04::/64
2001:D12:AA04:B5::/64*
28. Which type of IPv6 address is not routable and used only for communication on a single subnet?
global unicast address
link-local address*
loopback address
unique local address
unspecified address
29. Which address type is not supported in IPv6?
private
multicast
unicast
broadcast*
30. What is the minimum configuration for a router interface that is participating in IPv6 routing?
to have only a link-local IPv6 address*
to have both an IPv4 and an IPv6 address
to have a self-generated loopback address
to have both a link-local and a global unicast IPv6 address
to have only an automatically generated multicast IPv6 address
31. A user calls to report that a PC cannot access the internet. The network technician asks the user to issue the command ping 127.0.0.1 in a command prompt window. The user reports that the result is four positive replies. What conclusion can be drawn based on this connectivity test?
The PC can access the network. The problem exists beyond the local network.
The IP address obtained from the DHCP server is correct.
The PC can access the Internet. However, the web browser may not work.
The TCP/IP implementation is functional.*
32. Which command can be used to test connectivity between two devices using echo request and echo reply messages?
netstat
traceroute
ICMP
Ping*
33. What field content is used by ICMPv6 to determine that a packet has expired?
TTL field
CRC field
Hop Limit field*
Time Exceeded field
34. Which protocol provides feedback from the destination host to the source host about errors in packet delivery?
ARP
BOOTP
DNS
ICMP*
35. Which utility uses the Internet Control Messaging Protocol (ICMP)?
RIP
DNS
Ping*
NTP
36. A network administrator can successfully ping the server at www.cisco.com, but cannot ping the company web server located at an ISP in another city. Which tool or command would help identify the specific router where the packet was lost or delayed?
ipconfig
netstat
telnet
traceroute*
37. Which protocol is used by IPv4 and IPv6 to provide error messaging?
ICMP*
NDP
ARP
DHCP
38. What message is sent by a host to check the uniqueness of an IPv6 address before using that address?
neighbor solicitation*
ARP request
echo request
router solicitation
39. A technician is troubleshooting a network where it is suspected that a defective node in the network path is causing packets to be dropped. The technician only has the IP address of the end point device and does not have any details of the intermediate devices. What command can the technician use to identify the faulty node?
Tracert*
ping
ipconfig /flushdns
ipconfig /displaydns
40. A user who is unable to connect to the file server contacts the help desk. The helpdesk technician asks the user to ping the IP address of the default gateway that is configured on the workstation. What is the purpose for this ping command?
to obtain a dynamic IP address from the server
to request that gateway forward the connection request to the file server
to test that the host has the capability to reach hosts on other networks*
to resolve the domain name of the file server to its IP address
41. What is a function of the tracert command that differs from the ping command when they are used on a workstation?
The tracert command reaches the destination faster.
The tracert command shows the information of routers in the path.*
The tracert command sends one ICMP message to each hop in the path.
The tracert command is used to test the connectivity between two devices.
42. Which ICMP message is used by the traceroute utility during the process of finding the path between two end hosts?
redirect
ping
time exceeded*
destination unreachable
43. Which two things can be determined by using the ping command? (Choose two.)
the number of routers between the source and destination device
the IP address of the router nearest the destination device
the average time it takes a packet to reach the destination and for the response to return to the source*
the destination device is reachable through the network*
the average time it takes each router in the path between source and destination to respond
44. Which statement describes a characteristic of the traceroute utility?
It sends four Echo Request messages.
It utilizes the ICMP Source Quench messages.
It is primarily used to test connectivity between two hosts.
It identifies the routers in the path from a source host to a destination host.*




provide the first and the last subnet ID when the subnet prefix is /53, /55, /59/, 63 when the initial subnet is 2001:EF3:BAC1::/49
thankyou for information